[ad_1]
Countries in Europe, the Middle East and Africa are taking note: The European Commission plans to set up a Joint Cyber Unit to combat large-scale cyberattacks. The Saudi Arabian government launched the National Cyber Security Authority to improve the country’s cybersecurity stance. The African Union has identified cybersecurity as part of its Agenda 2063 to transform Africa.
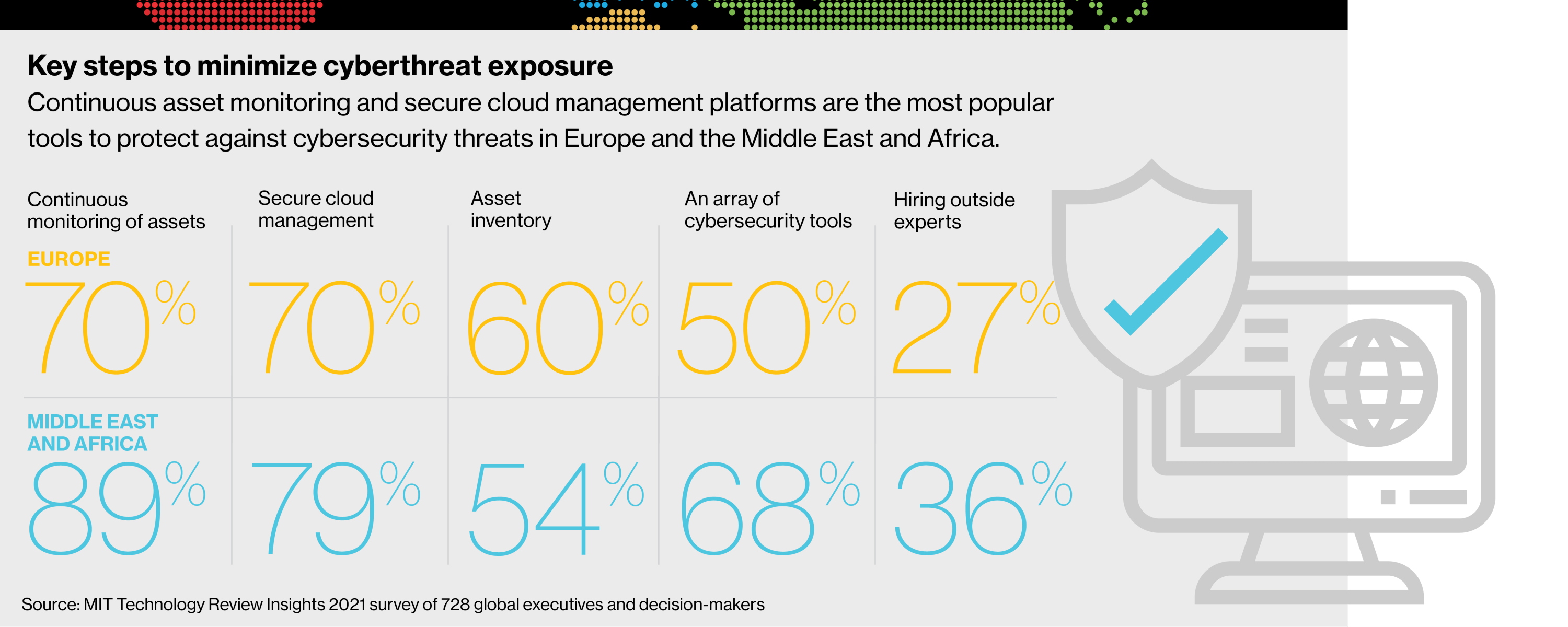
MIT Technology Review Insights and Palo Alto Networks surveyed 728 people to explore the challenges facing today’s cybersecurity teams and the strategies they should adopt to protect the attack surface (the sum of the points an unauthorized user can use to access an organization’s systems). business leaders. The survey was global, with 38% of respondents from Europe and 13% from the Middle East and Africa. Industry experts’ responses, along with input, provide a solid framework for guarding against growing bad actors and fast-moving threats.
But organizations themselves can take critical steps to better understand, in an intelligent, data-driven way, where attacker entry points are in information technology (IT) environments.

Vulnerabilities of a cloud environment
The cloud continues to play a critical role in accelerating digital transformation. And for good reason: the cloud offers solid benefits such as increased flexibility, cost savings, and greater scalability. Cloud-based environments though 79% of observed exposuresCompared to 21% for on-premises assets, according to the “2021 Cortex Xpanse Attack Surface Threat Report.”
This is alarming, given that 53% of respondents in Europe and 48% in the Middle East and Africa report that more than half of their assets are in the cloud.
“Many companies started their cloud journey because it made sense,” says Amitabh Singh, chief technology officer for Europe, the Middle East and Africa at Cortex, Palo Alto Networks’ security operations platform division. But there are pitfalls, he says.
“With the cloud, the high wall around organizations’ core assets and infrastructure melted away. As a result, some assets that companies consider safe may be exposed to security vulnerabilities.”
Of course, there are technologies that can improve cloud security. But Singh says many organizations in Europe have been slow to adopt more innovative tools. “I still see companies struggling with legacy antivirus and anti-malware platforms,” he says.
Remote work has also contributed to increased cybersecurity risks for cloud environments. Remote workers rely on the cloud to do their work, such as texting with colleagues, collaborating on projects, or videoconferencing with customers. And now when physically removed IT isn’t responsive to their needs, remote workers can easily buy their own online solutions to problems. This is what is known as shadow IT: it bypasses normal cybersecurity practices and opens up a world of concern for IT teams.
Ask Chris Sandford, manager of industrial cybersecurity services at Applied Risk, an industrial cybersecurity consultancy in the Netherlands. While work-from-home arrangements have long been common in Northern Europe, Sandford says there are “many companies that are not prepared for remote working and the associated challenges and vulnerabilities” when the 2020 coronavirus pandemic forces many workers to work from home. Case study: The majority of respondents in Europe (53%) say they have experienced a cybersecurity attack, with 35% in the Middle East and Africa originating from unknown, unmanaged or poorly managed digital assets.
Sandford provides a hypothetical example of an employee using an unsecured cloud server to access business applications without the necessary authentication or authorization measures. “How do you know someone didn’t come back from that cloud to your own network?” He asks. “There is very limited visibility or understanding of this cloud service.”
A strong action plan
Fortunately, there are steps organizations in Europe, the Middle East and Africa can take to minimize exposure to cybersecurity threats and take control of their cloud environments. Most respondents in Europe (70%) and the Middle East and Africa (89%) rely on continuous asset tracking technology for protection. Gone are the days when companies could take an ad hoc approach to identifying security risks.
“In the good old days, we used to regularly scan our infrastructure, find vulnerabilities, and then patch them while managing vulnerabilities,” Singh says. “Now, we don’t have the luxury of time. If there are vulnerabilities and we cannot manage them almost instantaneously, bad actors can exploit them.”
Download full report.
This content is produced by Insights, the exclusive content arm of MIT Technology Review. It was not written by the editorial staff of MIT Technology Review.
[ad_2]
Source link

